-

What is a Buffer Overflow? Do These of Attacks
-

Buffer Overflow Lab.docx - Buffer Overflow Lab Based heavily a lab developed by Wenliang Du of Syracuse University as part of the SEED labs series | Course Hero
-
Buffer Overflows: Attacks and Defenses the Vulnerability of the Crispin Cowan SANS download
-
Study 3 Shark Attack Adapted from the
-
overflow explained
-

Buffer Overflow Lab.docx - Buffer Overflow Lab Based heavily a lab developed by Wenliang Du of Syracuse University as part of the SEED labs series | Course Hero
-
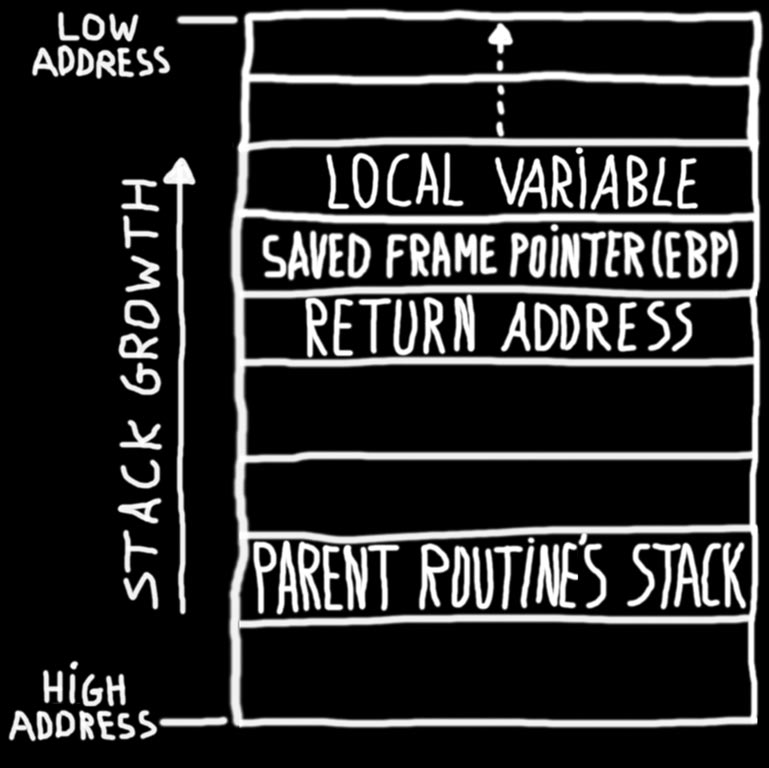
overflow explained
-

Buffer_Overflow - COMP293 Buffer Vulnerability 1 Buffer Overflow Vulnerability Lab 1 Lab Overview The learning objective of this lab is to | Course Hero
-
A DataCentric Approach to Attack Detection in
-

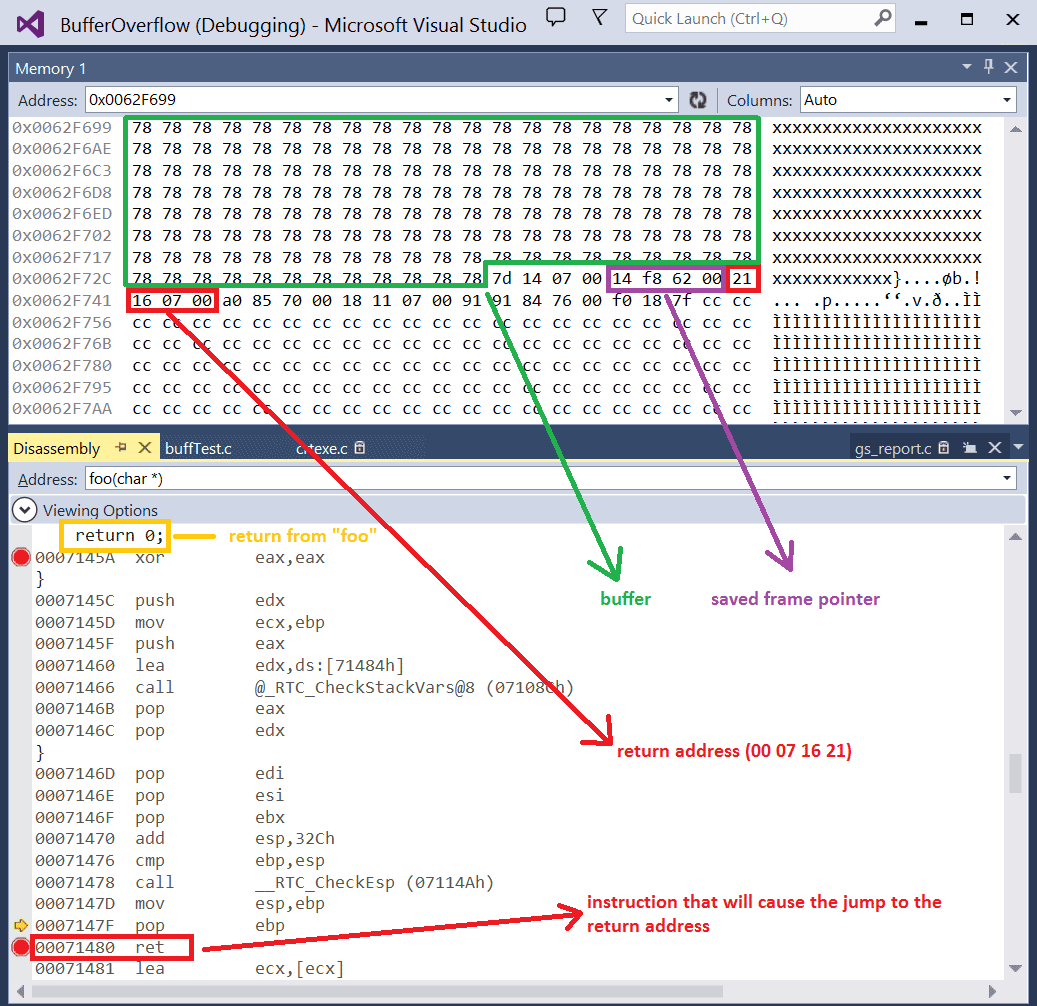
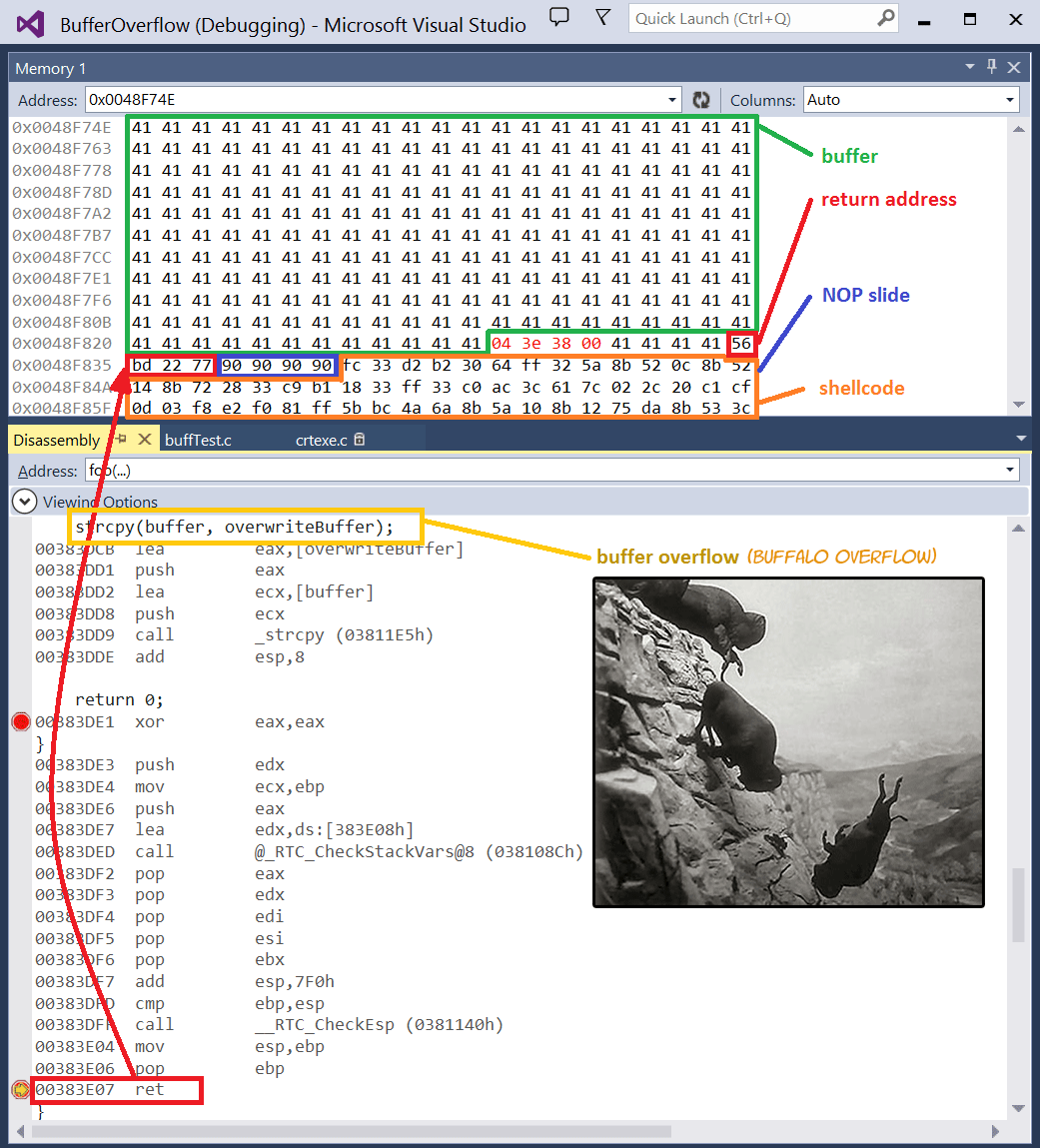
Lab 3 report.docx - Ankit Kumar 773312668 Buffer Vulnerability Lab Report Task 1 Non-root stack program Debug stack 1.1 Return address | Course Hero
-
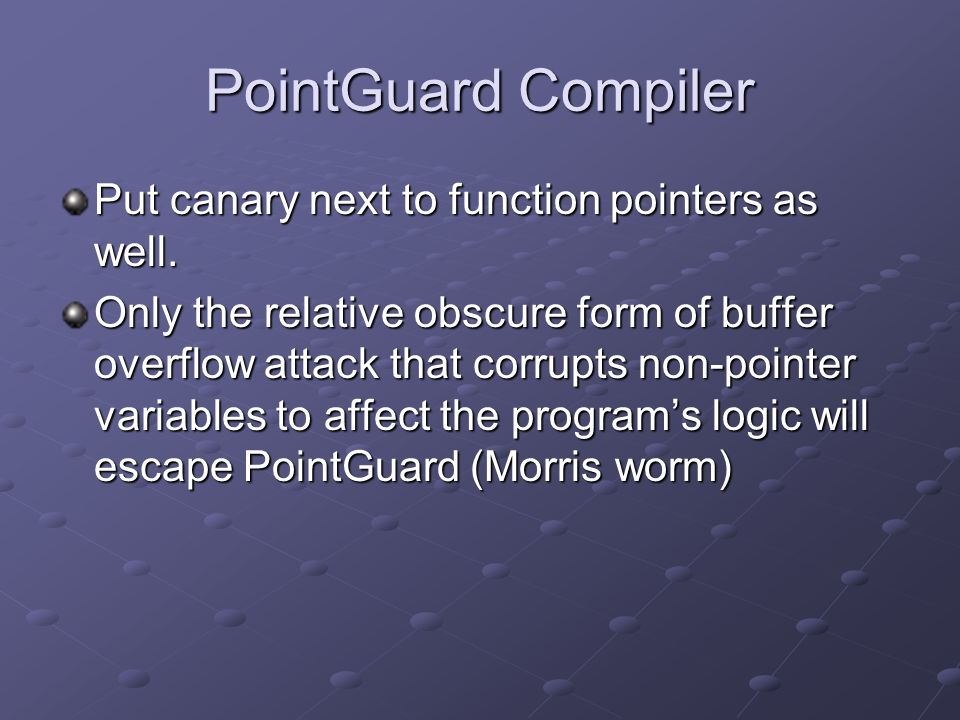
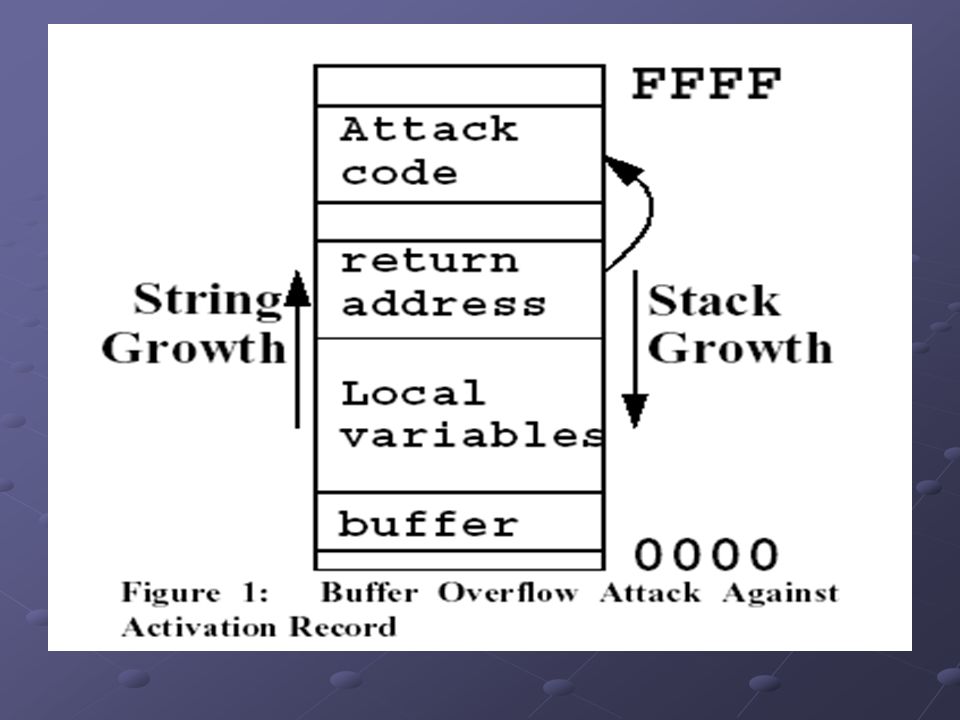
Information and Computer Security Shambhu Upadhyaya CSE
-
overflow explained
-
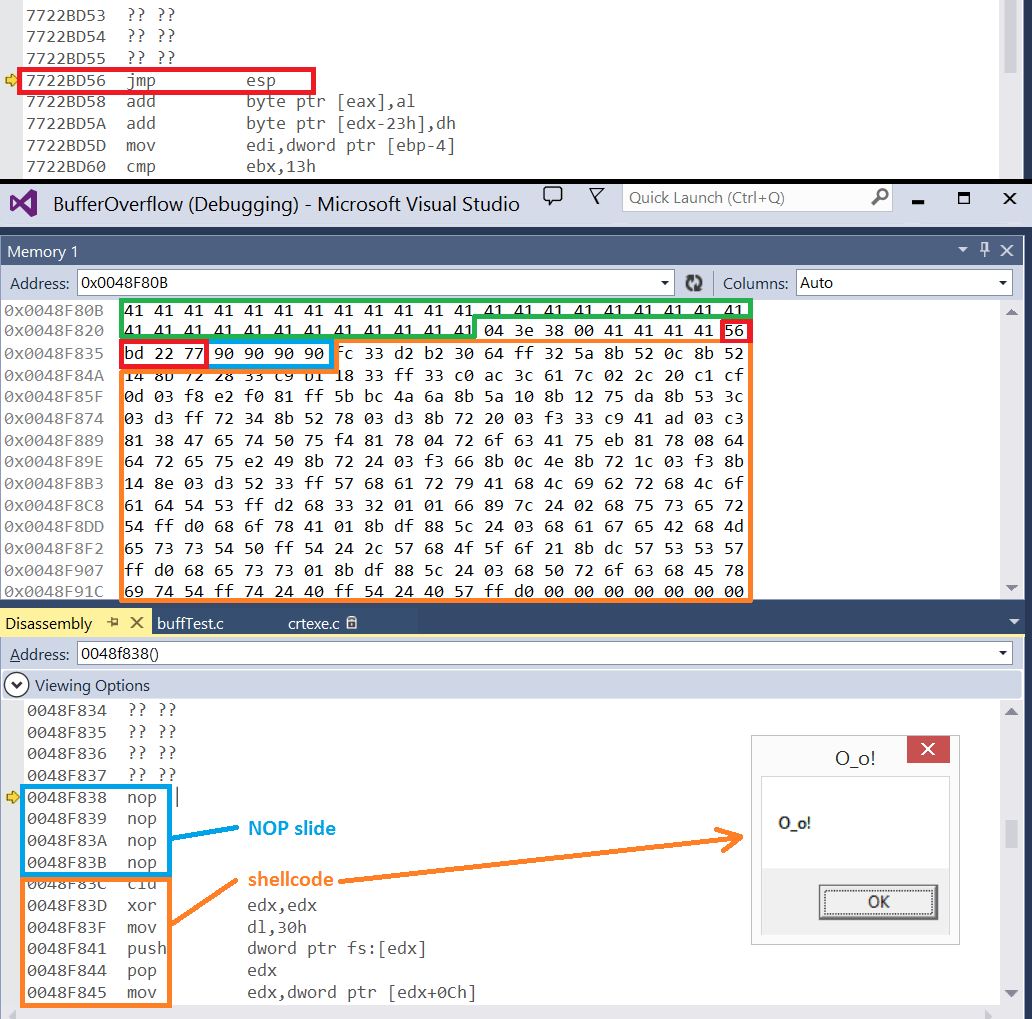
Understand and Exploit Buffer Overflow by Sec…
-
overflow explained
-
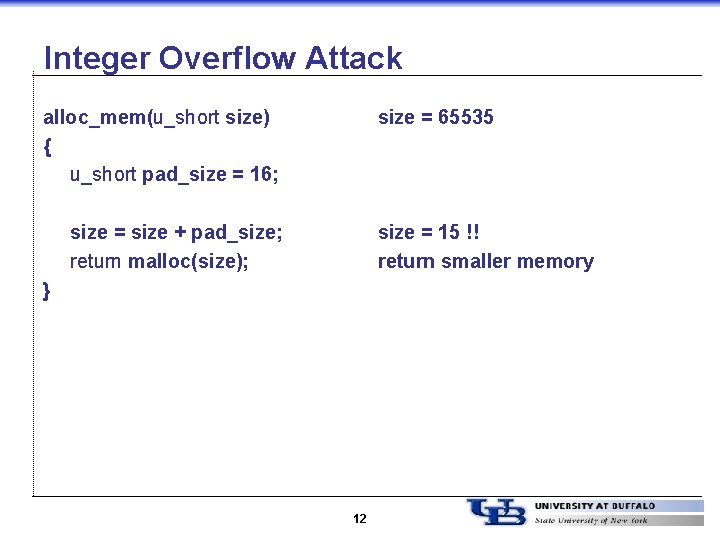
Information and Computer Security Shambhu Upadhyaya CSE
-
overflow explained
-

is a Buffer Overflow Attack Types and Prevention Methods | Imperva
-

Buffer Overflow Lab.docx - Buffer Overflow Lab Based heavily a lab developed by Wenliang Du of Syracuse University as part of the SEED labs series | Course Hero
-

What is a Buffer Overflow? Do These of Attacks
-

Buffer_Overflow - COMP293 Buffer Vulnerability 1 Buffer Overflow Vulnerability Lab 1 Lab Overview The learning objective of this lab is to | Course Hero
-
overflow explained
-

An introduction to computer buffer overflow on using unsecured C or C++ standard functions in C programs
-
buffer - ppt download
-

The Sleepy History of the Buffer Overflow | Legaltech News
-
Buffer Overflows: Attacks and Defenses the Vulnerability of the Crispin Cowan SANS download
-
Buffer Overflow and Buffer Overflow Attack Prevention - Logsign